How does an SRX Series device examine exception traffic?
Correct Answer:
A
Exception traffic, including management and control plane traffic, is handled by examining host-inbound traffic configurations at the ingress interface and zone. It ensures traffic reaches necessary services like SSH and IKE securely. See Juniper Host Inbound Traffic Documentation for more.
SRX Series devices handle exception traffic (such as management traffic like SSH, Telnet, DNS queries, etc.) differently than regular transit traffic. Exception traffic is examined based
on host-inbound traffic for the ingress interface and zone. If traffic is destined for the device itself (e.g., management traffic or routing protocol messages), it must be allowed as host-inbound traffic on both the ingress interface and zone.
Example Command: bash
set security zones security-zone trust host-inbound-traffic system-services ssh
This ensures that traffic destined to the SRX device is inspected based on the ingress interface and zone.
: Juniper documentation on host-inbound traffic and exception handling.
==========
You are asked to configure tenant systems.
Which two statements are true in this scenario? (Choose two.)
Correct Answer:
CD
Each tenant system maintains its own configuration database, isolating configurations from others, enhancing security and operational efficiency. Junos OS supports multiple concurrent commit operations across tenant systems. Further details are covered in the Juniper Tenant System Guide.
When configuring tenant systems on an SRX device, the following principles apply:
✑ Tenant Systems Have Their Own Configuration Database (Answer C): Each tenant system has its own isolated configuration database, ensuring that changes made in one tenant system do not affect others. This allows for multi-tenant environments where different tenants can have independent configurations.
✑ Commit Multiple Tenant Systems Simultaneously (Answer D): The system allows for multiple tenant systems to be committed at the same time, simplifying management when working with multiple tenants. This is particularly useful in large environments where multiple logical systems or tenants need updates simultaneously.
: Juniper documentation on tenant systems and configuration databases.
==========
Exhibit: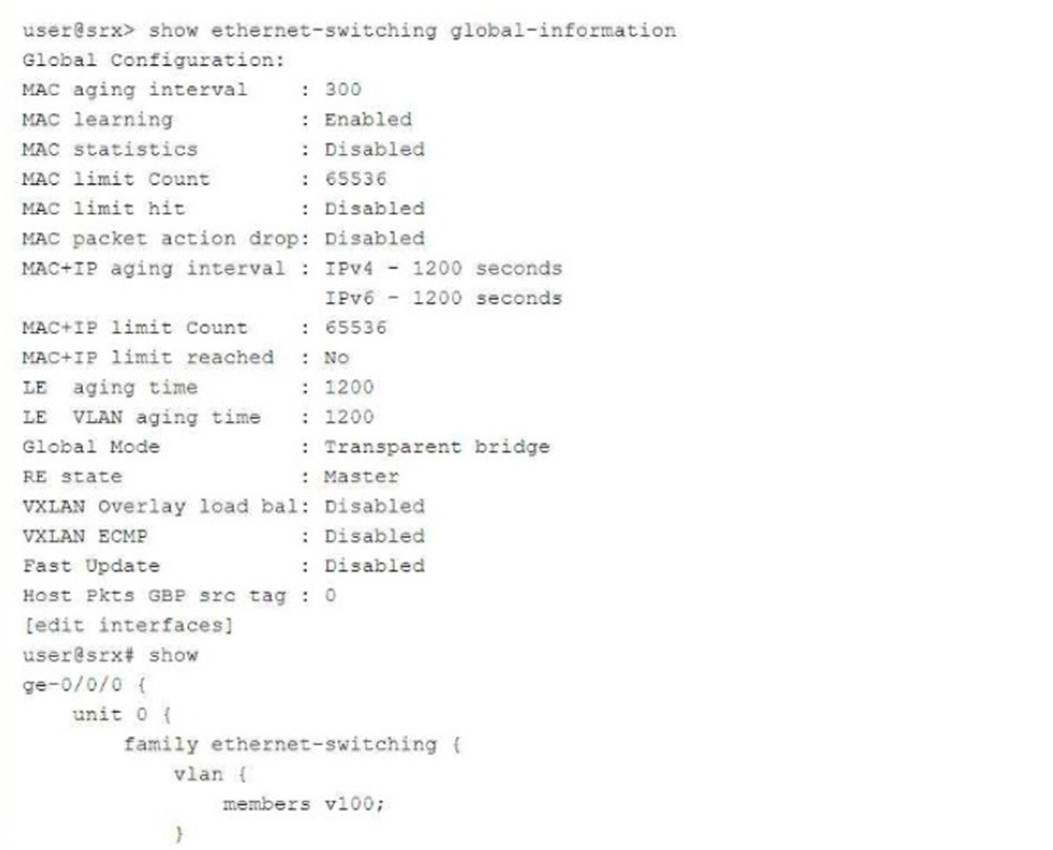
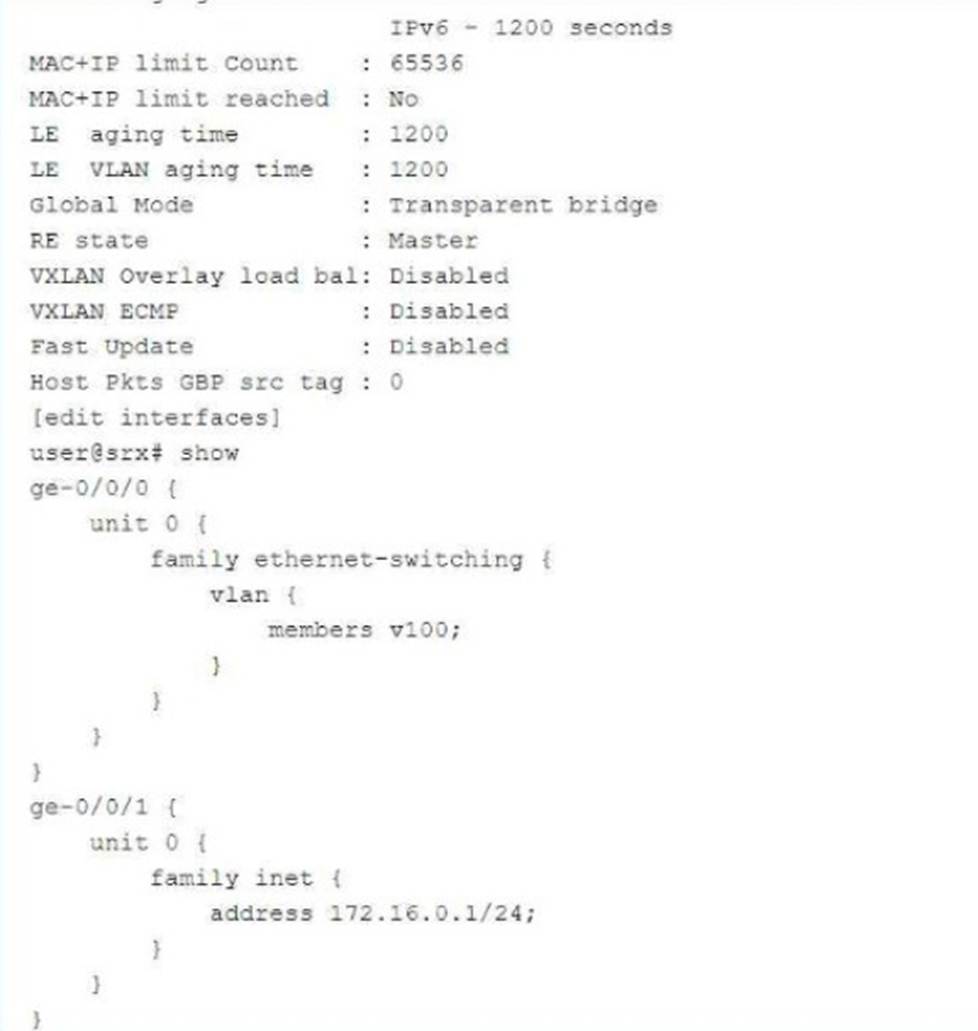
In which mode is the SRX Series device?
Correct Answer:
C
Which two elements are necessary to configure a rule under an APBR profile? (Choose Two)
Correct Answer:
BC
Here's why those elements are necessary for configuring a rule under an APBR profile:
✑ B. Match condition: This defines the criteria for matching traffic to the APBR rule. It can include:
✑ C. Then action: This specifies the action to take when traffic matches the rule. The primary action in APBR is:
Why other options are incorrect:
✑ A. Instance type: While routing instances are used in APBR, the "instance type" itself is not configured within the APBR rule. You define the instance type separately when configuring the routing instance.
✑ D. RIB group: RIB groups are used for route management and are not directly involved in APBR rule configuration.
You are deploying threat remediation to endpoints connected through third-party devices. In this scenario, which three statements are correct? (Choose three.)
Correct Answer:
ABD
For threat remediation in a third-party network, the RADIUS protocol is necessary to communicate with the RADIUS server for details about infected hosts. CoA enables security measures to be enforced based on endpoint information provided by the RADIUS server. Details on this setup can be found in Juniper RADIUS and AAA Documentation.
When deploying threat remediation to endpoints connected through third-party devices, such as switches, the following conditions must be met for proper integration and functioning:
✑ Explanation of Answer A (Support for AAA/RADIUS and Dynamic Authorization Extensions):
✑ Explanation of Answer B (Connector Gathers MAC Information via API):
✑ Explanation of Answer D (Connector Initiates CoA):
Juniper Security Reference:
✑ Threat Remediation via RADIUS: Dynamic remediation actions, such as CoA, can be taken based on information received from the RADIUS server regarding infected hosts. Reference: Juniper RADIUS and CoA Documentation.
==========

